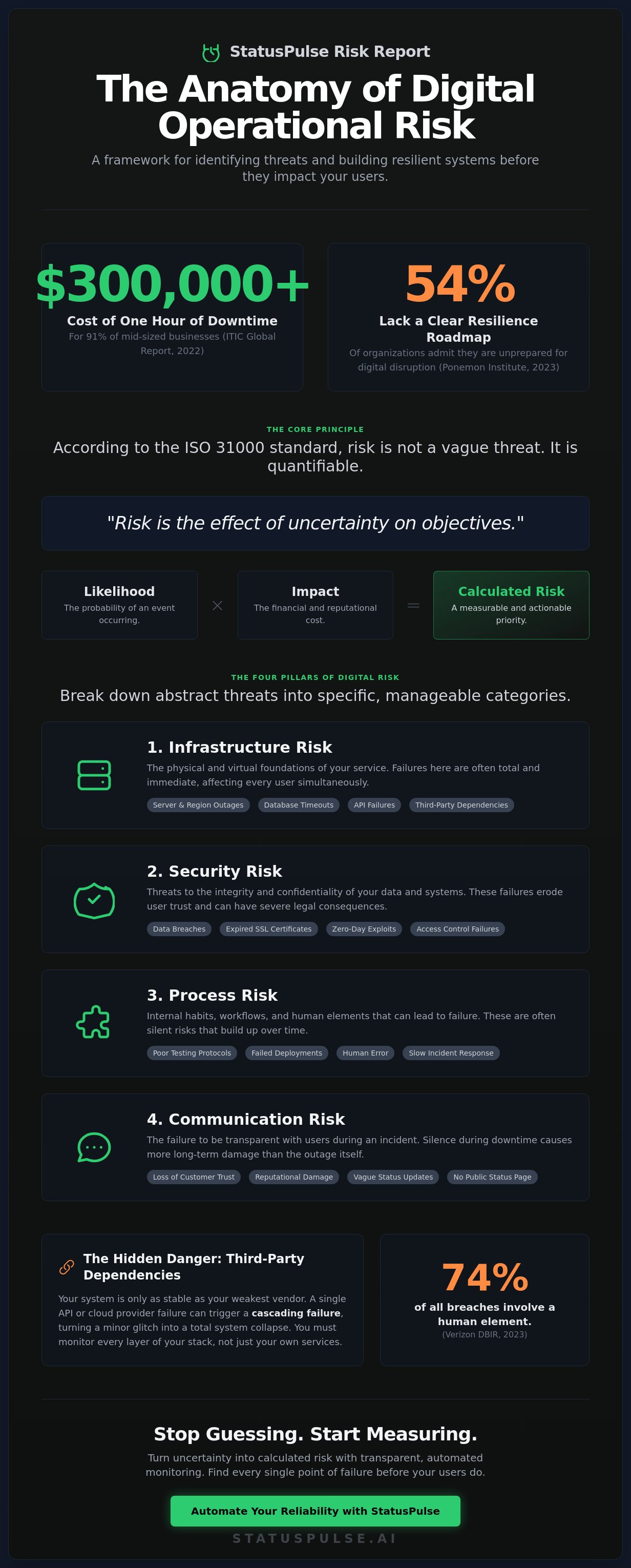
According to ITIC's 2022 Global Server Hardware report, a single hour of server downtime now costs over $300,000 for 91% of mid-sized businesses. You likely already feel this pressure. Vague corporate definitions of Risks don't help when your dashboard turns red at 3:00 AM. It's frustrating to manage hidden system vulnerabilities while incumbents hide behind complex jargon and bloated contracts. You know the cost of the unknown is high, but quantifying it for the board often feels like a guessing game. You deserve a clearer, more honest view of your infrastructure.
We'll show you how to master the fundamentals of risk management to protect your digital operations. Since 54% of organizations admit they lack a clear roadmap for digital resilience according to a 2023 Ponemon Institute study, this guide provides the necessary structure. You'll get a clear framework for categorizing threats and practical steps to mitigate outages before they start. You'll learn how to justify transparency tools to your team and build a resilient system that respects both your time and your users. We aren't here for corporate bloat. We're here for simple, effective solutions that keep your services running and your team calm. Let's look at the data.
Key Takeaways
- Master the ISO 31000 standard to distinguish between quantifiable Risks and unquantifiable uncertainty.
- Identify the four pillars of digital operational risk to protect your infrastructure from silent failures.
- Discover why uncommunicated outages cause more than just financial loss—they decay long-term customer trust.
- Implement a 5-step framework to find every single point of failure before your users do.
- Learn how to automate your reliability with an honestly priced, GDPR-native approach to monitoring.
What is Risk? Defining Uncertainty in the 2026 Landscape
Risk isn't a vague feeling of dread. The ISO 31000 standard defines it clearly: risk is the effect of uncertainty on objectives. In the 2026 landscape, this definition matters more than ever. It means any deviation from your expected path, whether positive or negative, counts as a factor. For a lean engineering team, a risk is anything that pulls focus from the product roadmap or threatens the integrity of user data. Managing these Risks requires a shift from reactive firefighting to proactive system design.
We must distinguish between risk and uncertainty. Risk is quantifiable. You can look at three years of server logs and calculate the probability of a database timeout. You can assign a number to it. Uncertainty is unquantifiable. It's the "unknown unknown," like a sudden change in EU data sovereignty laws or a black-swan event affecting global subsea cables. Effective risk management involves turning as much uncertainty as possible into measurable risk.
The math is simple: Risk = Likelihood x Impact. If a minor UI glitch happens daily but doesn't stop a user from converting, it's a low priority. If a total region outage has a 0.1% chance of happening but would cost the company €50,000 in hourly revenue, it's a critical priority. We don't guess. We calculate. This logic is why statuspulse.ai focuses on transparency; you can't calculate impact if you're hiding the data.
The Evolution of Risk: From Finance to DevOps
Risk used to live in bank vaults and insurance ledgers. Today, it lives in your CI/CD pipeline. The primary Risks in 2026 are digital availability and latency. A 500ms increase in TTFB (Time to First Byte) can lead to a 7% drop in conversions according to industry benchmarks. We've moved from protecting physical assets to maintaining digital uptime.
Zero risk is a myth. In complex distributed systems, something is always broken. A multi-region Jamstack setup might have a failing node right now, but the system stays up. We accept partial failure to avoid total collapse. This is the reality of modern infrastructure. We don't aim for perfection; we aim for resilience.
Objective vs. Subjective Risk Perception
Teams often ignore high-impact, low-likelihood events because they feel impossible. This is a psychological trap. We worry about a sophisticated zero-day exploit while our SSL certificates expire because someone forgot a calendar invite. We fear the wrong failures. Data from 2023 showed that 74% of all breaches included a human element, yet companies still spend 90% of their budget on automated tools.
Understanding your threshold is vital for growth. For a technical founder, Risk Appetite is the specific amount of operational turbulence you'll tolerate to maintain a competitive shipping velocity against bloated incumbents. You decide how much "breakage" is worth the speed of innovation. No surprises. Just honest trade-offs.
The Anatomy of Digital Operational Risk
Digital risk is not a single, looming cloud. It is a collection of specific points where your system meets reality. To manage these Risks, you must dismantle them into four distinct pillars. Infrastructure, Security, Process, and Communication. Infrastructure covers your physical and virtual foundations, like server stability and API health. Security focuses on the integrity of your data and the validity of your certificates. Process defines your internal habits, from testing protocols to incident response. Communication is the bridge of trust you build with your users when things inevitably go sideways.
Infrastructure risks often hide in plain sight. A server outage in a primary region can halt operations instantly. However, modern systems also rely on complex webs of API failures and third-party dependencies. If your payment processor or your database provider goes down, your site goes down too. These are the foundations you must monitor with technical precision. We believe in a grounded approach. You need to see the status of every layer, not just the front end.
The Hidden Danger of Third-Party Dependencies
Your risk profile includes every API and cloud provider in your stack. You are only as stable as your weakest vendor. When one small service fails, it can trigger a cascading failure. This chain reaction turns a minor glitch into a total system collapse. Developers need a strategy to handle these external vulnerabilities. You can find a detailed path forward in our API Monitoring guide. We prioritize integrity over flashiness. Knowing exactly which dependency is failing allows you to act with quiet confidence rather than panic.
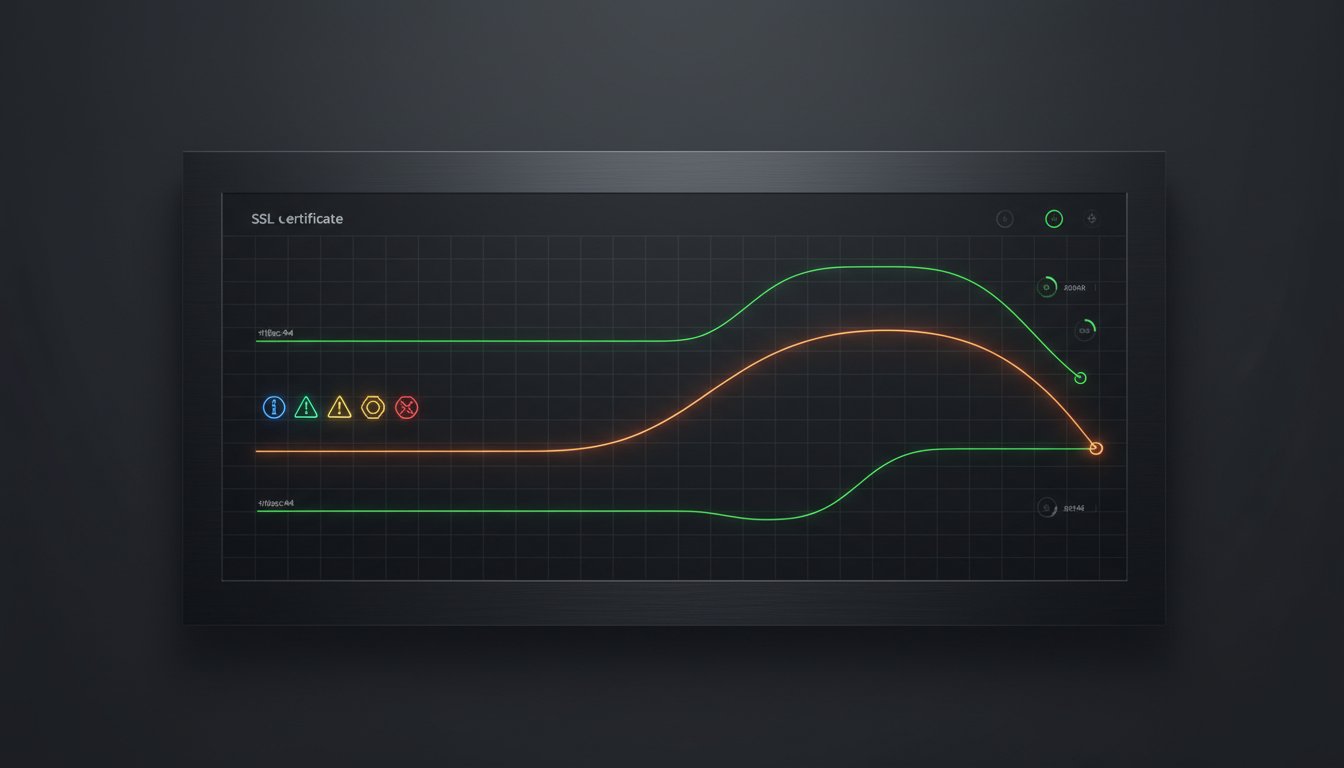
SSL and Domain Risks: The Silent Killers
A "Connection Not Private" warning is a reputational disaster. It signals to your customers that you are no longer paying attention. Most of these errors are the result of simple human oversight; a renewal date was missed or a calendar invite was ignored. Automation reduces the risk of human error by handling certificate renewals and domain checks programmatically. The financial stakes are high. IBM reported that the average cost of a data breach reached $4.45 million in 2023. While a simple outage might seem less severe, Gartner estimates that downtime costs businesses $5,600 per minute on average. These Risks are too expensive to leave to manual processes.
Process risks are often the most difficult to spot. Deploying code without rigorous testing is a gamble that rarely pays off. Many teams utilize the NIST Risk Management Framework to establish a structured approach to these internal threats. It provides a logical path to identify, protect, and recover from operational failures. Without a clear incident response plan, your team will waste valuable minutes during a crisis. We built StatusPulse to be the tool you use when those minutes matter most. It is honestly priced and designed to keep your communication as streamlined as your code.
Financial vs. Reputational Risk: The Cost of Silence
Downtime isn't just a technical glitch. It's a balance sheet event. When your service drops, the clock starts ticking. For a mid-market enterprise, the average cost of downtime is often cited at $5,600 per minute by industry analysts like Gartner. These Risks manifest as immediate SLA credits, lost sales, and abandoned carts. But the immediate financial hit is only the surface. The hidden cost is churn. A single uncommunicated outage can increase customer turnover by 30% in the following quarter. Users don't leave because of a bug; they leave because they feel ignored.
Reputational risk is a slow decay. We see many incumbents lean into "Dark Outages." This happens when a company stays silent while their dashboard shows green. It's a gamble that customers won't notice. They always do. This silence breaks the psychological contract between a developer and a service provider. Contrast this with transparent incident communication. Admit the mistake early. Provide the technical details. This creates the "Honesty Dividend." When you're upfront about failure, you actually build loyalty. Transparency proves you're in control even when the systems aren't.
Quantifying the ROI of Transparency
Calculating the cost of downtime requires looking at your specific tiers. If you have 1,000 customers on a €50 monthly plan, one hour of 100% downtime costs roughly €70 in direct revenue. That's manageable. The real danger is the support queue. A public status page at statuspulse.ai can reduce ticket volume by 65% during a high-risk event. It stops the "Is it just me?" emails before they start. Silence is the loudest message you can send during a crisis. It tells your users that you're either unaware of the problem or you're hiding it. Neither builds a sustainable business.
Incident Communication as Risk Mitigation
A public status page is an insurance policy for your brand. It moves your team from reactive panic to proactive management. Part of this involves a thorough Digital Identity Risk Assessment to understand how access failures impact your total risk profile. You must distinguish between "Marketing Transparency" and "Technical Honesty." Marketing is about optics. Technical honesty is about the facts. It's about multi-region latency and Jamstack deployments.
We believe in removing the emotional friction of crisis management. When the server room is on fire, the last thing you want to do is draft a perfect update. We use AI to handle the heavy lifting. Claude drafts the update based on your technical logs. You press send. It's that simple. By automating the communication, you mitigate the Risks of human error and delay. You stay calm. Your customers stay informed. Your brand stays intact.
- Direct Loss: SLA credits and lost transactions.
- Churn: Long-term revenue decay from lost trust.
- Support Load: The operational cost of a flooded inbox.
- Brand Value: The difference between an "honest" provider and a faceless incumbent.
Our approach is grounded in ethics and efficiency. EU-hosted. GDPR-native. Honestly priced. We don't believe in corporate bloat or complex pricing. We believe in getting the details right. No surprises. Just uptime.
Modern Risk Mitigation: A 5-Step Framework for Teams
Managing Risks in a digital environment isn't about avoiding every incident. It's about building systems that handle failure gracefully. Incumbents often sell complex, bloated frameworks that hide the truth behind layers of jargon. We prefer a lean, 5-step approach that focuses on technical integrity and honest communication. It's about being prepared, not just being lucky.
- Step 1: Identify. Don't wait for a manual audit. Use automated monitoring to map every single point of failure across your stack. If you don't see it, you can't fix it.
- Step 2: Analyze. Set clear thresholds. Determine the exact latency and uptime metrics that trigger an alert. If a response takes longer than 500ms, your team needs to know immediately.
- Step 3: Evaluate. Not all failures are equal. Prioritize risks based on their direct impact on the user experience. A broken checkout process is always more urgent than a missing footer icon.
- Step 4: Treat. Build resilience. Implement automated failovers and multi-region redundancies. If one server goes dark, another should take its place without human intervention.
- Step 5: Monitor & Communicate. Stay transparent. Ensure stakeholders receive real-time updates through a public status page. Honesty builds more trust than a perfect record ever could.
Proactive vs. Reactive Monitoring
Waiting for a user to report a bug is the highest-risk strategy a team can adopt. By the time a support ticket arrives, you've already lost trust. Data from the Uptime Institute in 2023 shows that 55 percent of operators experienced a significant outage in the last three years. Many of these incidents could have been mitigated by catching micro-outages early. Implementing 1-minute uptime checks allows you to spot transient errors that 5-minute intervals miss. For a deeper dive into technical reliability, read our Uptime Monitoring Guide.
Building a Culture of Post-Mortems
Every realized risk is a data point. When a system fails, the goal isn't to find someone to blame. Blameless post-mortems reduce the risk of future human error by focusing on systemic weaknesses rather than individual mistakes. Documentation acts as a tool for long-term risk reduction. It turns a stressful incident into a permanent improvement for the team. We believe in getting the details right. This means recording exactly what happened and how to prevent it next time. No fluff. Just better code and a more resilient infrastructure.
Protect your uptime with a tool built for developers. Get started with StatusPulse.
Reducing Risk with StatusPulse: Honestly Priced Reliability
Risk management shouldn't be a manual chore. Most engineering teams lose hours every month to tedious monitoring tasks. StatusPulse changes that by automating the most frustrating parts of the process. We built this for developers who want reliability without the noise. Our platform handles the heavy lifting so you can focus on building your product.
Data privacy is a significant factor in modern Risks. Many tools store your data in jurisdictions with weak protections or complex legal requirements. StatusPulse is different. Our infrastructure is entirely EU-hosted and GDPR-native. This isn't a marketing checkbox. It's a core design principle that eliminates compliance headaches before they start. You get professional-grade monitoring without the legal baggage of US-based incumbents.
Communication during an outage is often where things fall apart. Stress leads to mistakes. Our AI-powered updates solve this problem. Claude drafts the message for you based on the incident data. You press send. It keeps your customers informed while you focus on the fix. This reduces communication friction and maintains user trust when things go wrong.
Native Monitoring for Modern Stacks
Global SaaS needs more than a single ping from a single city. Multi-region monitoring is vital to catch localized outages that others miss. A server might look healthy in London while failing for every user in New York. StatusPulse brings SSL, API, and Uptime monitoring into one honest dashboard. You get a clear view of your entire stack without switching between five different tools. You can set up your account and start seeing results in less than three minutes at https://statuspulse.ai.
The StatusPulse Difference
Don't get caught in the incumbent trap. Huge software providers often charge for complexity you don't need. They build for enterprise buyers and corporate committees, not the people actually using the tools. StatusPulse is for teams that value integrity and speed. We offer professional-grade monitoring for €5, not $29. Four plans. No surprises. No hidden fees or corporate bloat.
We are a small, focused team. We care about the details because we use these tools ourselves every day. Our goal is to make your life easier through technical precision and plain-spoken ethics. It's time to move away from faceless corporations and choose a partner that values your time and your budget. Start monitoring your risks for free with StatusPulse.
Build a Resilient Digital Future
Managing digital operations in the 2026 landscape requires a shift from reactive firefighting to proactive transparency. You've seen how the anatomy of operational failure leads to costs that go far beyond technical debt. By implementing a 5-step framework, your team can bridge the gap between financial stability and user trust. Navigating these Risks effectively means choosing tools that prioritize integrity over corporate bloat. It's about having a clear view of your infrastructure when every second counts.
StatusPulse is built by a small team of developers who care about getting the details right. It's EU-hosted and GDPR-native. This isn't another complex enterprise tool with hidden fees. It's a reliable, straightforward solution used by developers worldwide to stay ahead of outages. You get professional authority without the unnecessary noise of industry incumbents. Stay focused on building while we handle the monitoring. It's time to trade uncertainty for quiet confidence.
Eliminate the risk of unexpected downtime with StatusPulse. Honestly priced from €5/month. You're ready to lead your team toward a more stable and transparent digital presence.
Frequently Asked Questions
What are the four main types of risk in business?
Business risks fall into four categories: strategic, compliance, operational, and financial. The COSO 2017 framework identifies these as the core pillars of corporate stability. Strategic risks involve market shifts or failed business models. Compliance covers legal mandates like the GDPR. Operational risks stem from internal process failures. Financial risks involve capital loss or currency fluctuations. Every company faces these daily.
How is risk different from uncertainty?
Risk is quantifiable data, while uncertainty is a total lack of information. Frank Knight established this distinction in his 1921 work. You calculate risk using historical patterns and mathematical probability. Uncertainty doesn't provide enough data for a formula. It's the difference between a known gamble and a total unknown. In tech, we manage risks but we prepare for uncertainty.
What is a risk assessment in a technical environment?
A technical risk assessment maps your digital infrastructure to identify vulnerabilities. You analyze servers, databases, and third-party APIs for potential failure points. It's a meticulous process of documenting what could break and how much it hurts your users. We focus on regional compliance and latency to keep things stable. This assessment creates a roadmap for your engineering team to follow.
Can all risks be eliminated in a SaaS product?
You can't eliminate every risk in a SaaS environment. Residual risk exists even in the most hardened systems. A 99.9 percent uptime guarantee still allows for 8.77 hours of downtime every year. The goal is mitigation and transparency, not perfection. We build for resilience because total elimination is a marketing myth sold by incumbents. You plan for the inevitable.
How do you calculate the financial impact of a technical risk?
Calculate financial impact by multiplying the probability of a failure by the cost of the resulting downtime. Gartner reported in 2014 that the average cost of IT downtime is $5,600 per minute. If a specific risk has a 10 percent chance of occurring and would cost $100,000 in lost sales, its expected value is $10,000. Use these numbers to prioritize your security budget.
Why is communication considered a risk management tool?
Communication stops a technical glitch from becoming a total PR disaster. Transparent status pages keep users informed and reduce the load on your support team during an incident. When you share honest updates, you maintain user trust even during server outages. It's about being human and taking responsibility. Clear messaging is as important as the technical fix itself.
What is the "Risk Appetite" of a startup vs. an enterprise?
Startups have a high risk appetite to achieve rapid growth, whereas enterprises prioritize stability and asset protection. A startup might ship code with minor bugs to beat a competitor to market. An enterprise often spends 6 months on a security review before a single deployment. They value the status quo. One seeks disruption. The other seeks to avoid any surprises.
How does SSL monitoring reduce security risk?
SSL monitoring tracks certificate expiration dates to prevent sudden site outages and security risks. Keyfactor reported in 2021 that 80 percent of organizations experienced at least one certificate-related outage in the previous two years. Automated alerts ensure you renew certificates long before they expire. It's a simple way to maintain encrypted connections without the manual headache or the corporate bloat.